Welcome to the latest edition of Pardon The Intrusion, TNW’s bi-weekly newsletter in which we explore the wild world of security.
During the first wave of COVID-19, contact tracking apps were touted as THE BIG SOLUTION to tackle the pandemic.
Most countries have introduced their own versions, and later Apple and Google jointly created a unified exposure notification API that works for Android and iOS.
That’s all well and good, but there weren’t any indeed proofs nevertheless, they are helping to stop COVID-19.
Then there are the privacy and security concerns. Contact tracking apps often rely on Bluetooth and location tracking to warn people who have been around someone who test positive.
One such app is Aarogya SetuThis is the Government of India’s official nationwide coronavirus tracker.
After concerns were repeatedly raised about the app’s use of GPS data, eventually becoming the Android version of the app Open-Source im Mai (The iOS version has not yet been made available).
But apparently there is more to be feared. India Central information commission has now warned the country’s Department of Electronics and Information Technology (MeitY) of “obstruction of information and evasion” in response to questions from activist Saurav Das about the design of the app, including details of private sector involvement.
MeitY hat a Explanation In order to solve the problem, it was insisted that the app be developed in the most transparent way and that all details and documents, including privacy policy and Aarogya Setu Data access and knowledge sharing Logs. “
While it can’t be denied that contact tracking apps can be useful for tracking real-time spikes in exposures, transparency and accountability go a long way in building confidence in the technology.
What’s the trend in terms of security?
The gang behind Maze ransomware turn off, Bridgefy offline messaging app added End-to-end encryptionand NSA whistleblower Edward Snowden was granted permanent residence in Russia.
- WIRED’s Lily Hay Newman introduced Maddie Stone, who works for Google’s Project Zero elite bug-hunting team and who tracks down some of the most serious security vulnerabilities. “For me, the driving factor in my work is how cool it would be if everyone on earth, no matter how cheap or expensive their device was, had secure access to the Internet. That could spread to so many different parts of humanity, “says Stone. [WIRED]
- Another long read. This time from Signal CEO Moxie Marlinspike, who “tries to bring normalcy to the Internet”. [The New Yorker]
- NSA whistleblower and privacy activist Edward Snowden was given permanent residency in Russia. [Reuters]
- Bridgefy offline messaging app added support for end-to-end encryption two months after researchers discovered one Number of vulnerabilities This could be used to decanonymize users, decrypt and read direct messages, and even shut down the network. [TechCrunch]
- The group behind Maze Ransomware has finally ceased operations. [TechCrunch]
- Singapore has amended its Personal Data Protection Act (PDPA) to allow local businesses to use consumer data for selective purposes such as business improvement and research without prior consent. The revised regulation also allows tougher fines for data breaches above the previous limit of SG $ 1 million. [ZDNet]
- A data breach broker sells account databases with 34 million user records on behalf of a threat actor who broke into 17 companies this year. [Bleeping Computer]
- The DHS, CISA, and the FBI shared more information on how an Iranian state-sponsored hacking group was able to collect voter registration data from US state websites, including election sites. [CISA]
- Grayshift, the maker of the GrayKey device used by law enforcement to break into encrypted iPhones, raised $ 47 million. [Grayshift]
- The researchers managed to extract the secret key that encrypts the microcode updates provided by Intel to fix security holes and other types of bugs in its CPUs. [Ars Technica]
- The last 14 days of data breaches, leaks and ransomware: Dr. Reddys, Folksam, Gunnebo Group, Lazada RedMart, Mattel, Nitro PDF, About Steria, True, and Answering machine.
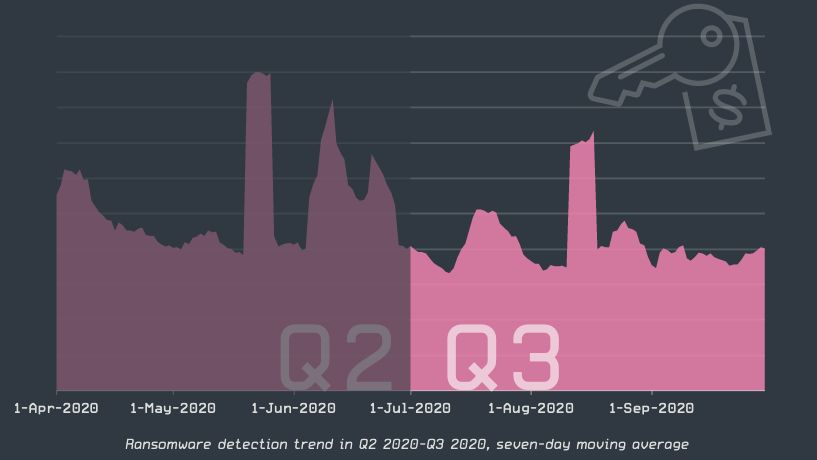
Data point
Even if the US government warns against it Ransomware attacks against health systems, cybersecurity company ESET Third Quarter 2020 Threat Report shows ransomware activity declined nearly 20% for the quarter. Based on telemetry data, Win / Filecoder.WannaCryptor led the category with more than 52% of detections. The Win / Filecoder.Crysis family took second place with 6.6%, followed by Win / Filecoder.Phobos with 4.7% of the detections.
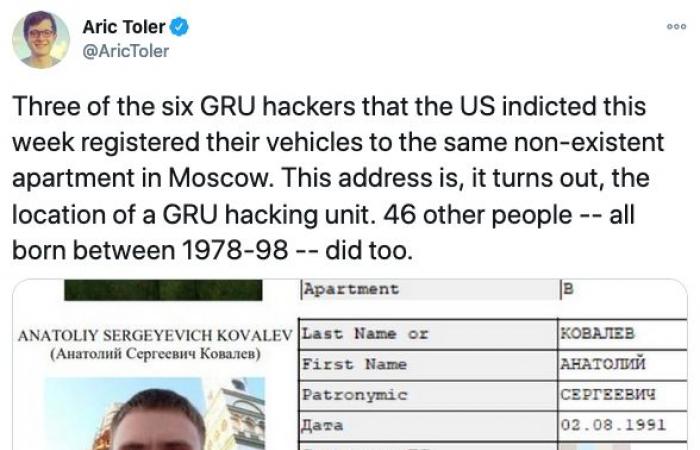
Tweet of the week
Talk about an Opsec bug! The US government 6 Russian intelligence officers charged last month for carrying out some of the most destructive cyber attacks. It turns out that three of the defendants and 46 others registered their vehicles in a nonexistent apartment in Moscow: “Freedom 21. ”

That’s it. I’ll see you all in two weeks. Stay safe!
Delighted x TNW (enthusiastic[at]the next web[dot]With)

These were the details of the news Your data is for sale for this day. We hope that we have succeeded by giving you the full details and information. To follow all our news, you can subscribe to the alerts system or to one of our different systems to provide you with all that is new.
It is also worth noting that the original news has been published and is available at de24.news and the editorial team at AlKhaleej Today has confirmed it and it has been modified, and it may have been completely transferred or quoted from it and you can read and follow this news from its main source.